Running Kubernetes in the Federal Government
Table of Contents

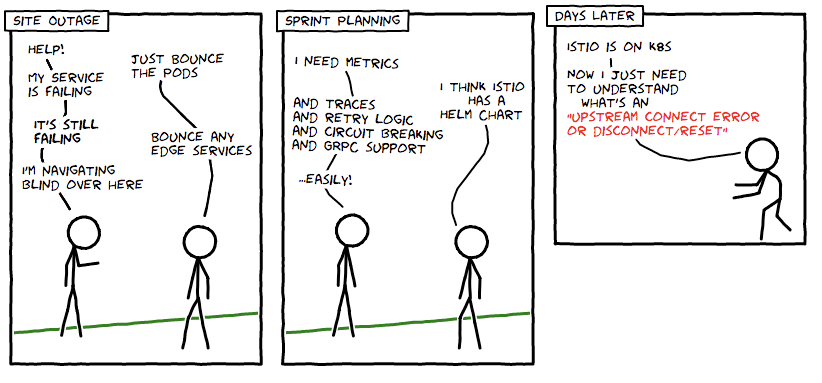
Tackling security compliance is a long and challenging process for agencies, systems integrators, and vendors trying to launch new information systems in the federal government. Each new information system must go through the Risk Management Framework (RMF) created by the National Institute of Standards and Technology (NIST) in order to obtain authority to operate (ATO). This process is often long and tedious and can last for over a year.
Open Control is a new standard by 18F, an agency bringing lean start-up methods to the U.S. Government, in order to address ATO repeatability. Red Hat has worked with 18F to help create a Kuberenetes implementation based on Open Control to automate much of the ATO process for Kubernetes systems.
Source: redhat.com