Using Gloo as an ingress gateway with Istio and mTLS (updated for Istio 1.1!)
Table of Contents
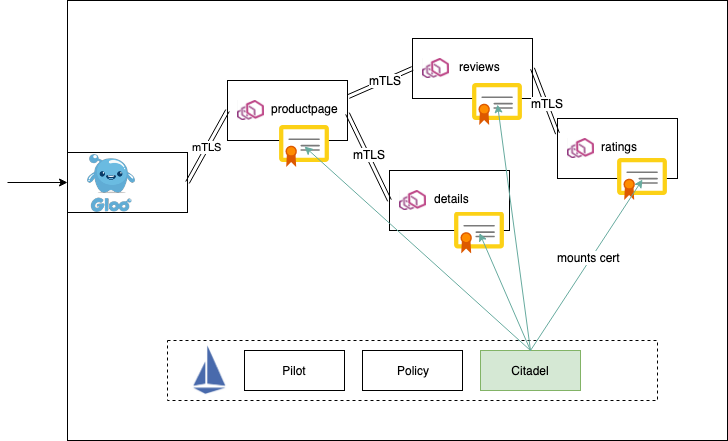
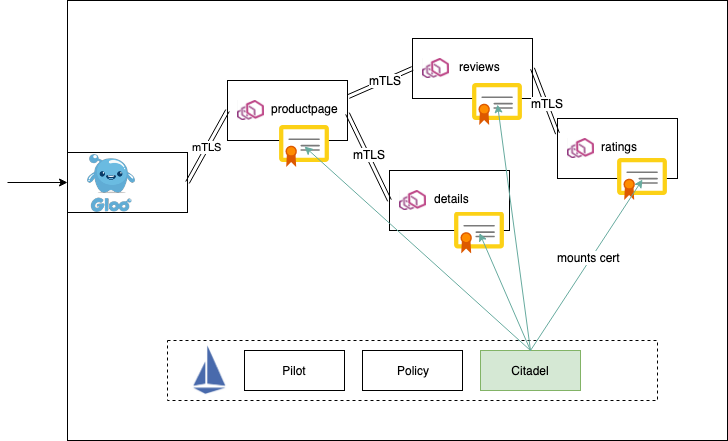
Istio is a popular open-source service mesh with powerful service-to-service capabilities such as request-routing control, metric collection, distributed tracing, security, et. al. Istio also ships with an ingress-gateway component that makes it easy to get traffic into your service mesh.
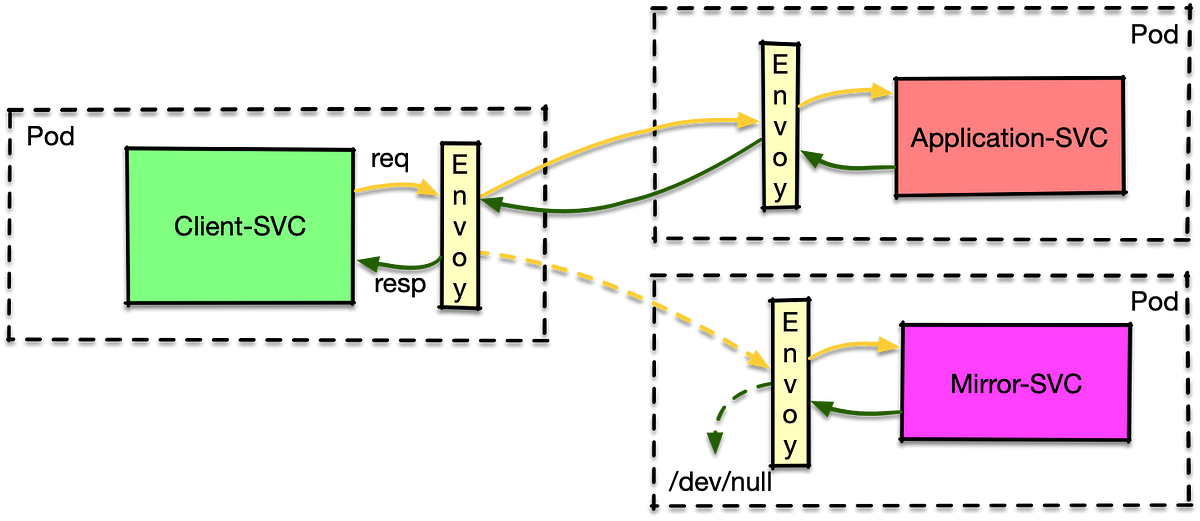
The Istio ingress gateway allows you to control what protocols, security requirements, and ports get exposed to the outside world, and then use Istio-native routing capabilities to route traffic to services. Gloo is an open-source API Gateway based on Envoy Proxy with advanced API Gateway capabilities like request/response transformation, function routing (Swagger, gRPC, cloud functions like Lambda, etc), a pluggable and extensible control plane and discovery system for Envoy, and more. As outlined in our “API Gateways are going through an identity crisis” blog, using an API gateway can give definition to your microservices, decouple front-end users/services from backend APIs, aggregate multiple APIs, and do more complex routing.
One of the more powerful features of Istio is the ability to securely authenticate and encrypt all traffic flowing over the mesh with mutual TLS. Gloo complements service-mesh technology like Istio and brings higher-level API capabilities to a service mesh. With Gloo, we can tie into Istio’s mTLS capabilities and route directly into the mesh for both Istio 1.0.x as well as the newly released Istio 1.1 (as of 3 hours ago at the time of writing!).
Let’s take a look.
Source: medium.com