Vault 1.1
Table of Contents
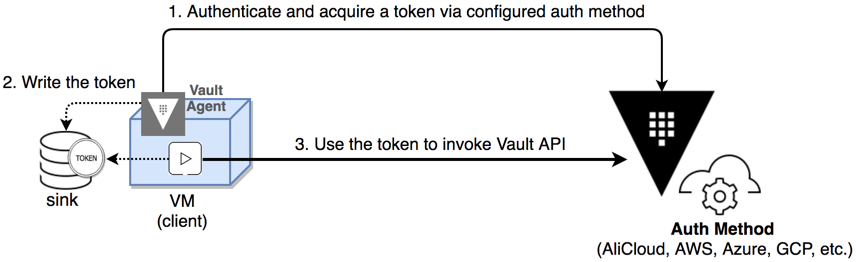
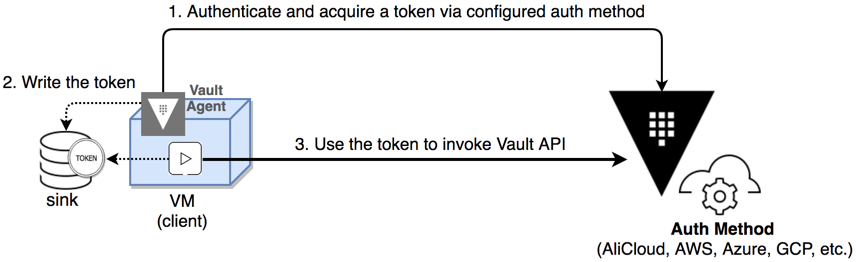
The release also includes additional new features, secure workflow enhancements, general improvements, and bug fixes. The Vault 1.1 changelog provides a full list of features, enhancements, and bug fixes. Vault agent now supports client-side caching of leased secrets.
An agent may now cache a response to a token managed client-side via auto auth. This allows for applications to work completely with Vault agent to manage a token’s lifecycle, simplifying edge computing use cases or use cases where encoding logic for an application to manage token expiry with a Vault cluster may be complicated (e.g.: bootstrapping an embedded system, container management use cases, etc.) There are many new features in Vault 1.1 that have been developed over the course of the 1.0.x releases.
We have summarized a few of the larger features below, and as always consult the changelog for full details: InfluxDB Database Plugin: Use Vault to dynamically create and manage InfluxDB users Group and Policy UI Search: Search for Group and Policy IDs when creating Groups and Entities instead of typing them in manually. Permissions-based UI Wizards: The Vault UI’s navigation and onboarding wizard now only displays items that are permitted in a users’ policy. ACL Path Wildcard: ACL paths can now use the + character to enable wild card matching for a single directory in the path definition.
cURL Command Output: CLI commands can now use the -output-curl-string flag to print out an equivalent cURL command. Response Headers From Plugins: Plugins can now send back headers that will be included in the response to a client.
The set of allowed headers can be managed by the operator.
Source: hashicorp.com
